IT-Security
Medialine Security: The pioneers for your IT security
Table of contents

Optimal protection for your valuable data and comprehensive security solutions from a single source. So you can concentrate on your core business.
Your IT security contact
Adrian Woizik is the managing director of Medialine Security GmbH and is responsible for developing and implementing comprehensive IT security strategies for companies. With over 25 years of experience in cybersecurity, he combines in-depth technical expertise with a strategic view of risks, compliance and cost-effectiveness. Together with his team, he supports companies in protecting their IT infrastructure in the long term – from security analysis and modern security architectures to managed security services.
Do you have any questions?
Cyber security is a complex topic, and every IT landscape has different requirements in terms of protection, processes and compliance. If you would like to learn more about our IT security solutions or would like an initial assessment of your current security situation, please do not hesitate to contact us. You can reach us by telephone on: +49 711 88770410, by email or via our contact form.

Medialine Security GmbH (formerly Thinking Objects GmbH)
Highest level of expertise in cyber security and cyber defence
With many years of experience and hundreds of customer scenarios under our belt, we offer you, as an ISO 27001-certified Managed Security Service Provider (MSSP), market-driven solutions to support, optimise and secure IT operations in large and medium-sized companies and corporations.
Comprehensive IT security is relevant for companies in many ways today: On the one hand, IT systems are exposed to a wide range of threats. The risk of data misuse is even greater due to wireless and mobile networking, as there are numerous points of attack within a single IT infrastructure. On the other hand, companies must arm themselves against a variety of different attack scenarios – especially since the motives of attackers are often financially driven. In addition, companies are required to comply with the provisions of the IT Security Act.

Comprehensive cyber security from the experts at Medialine Security
Companies must not only secure their data, applications, servers and data centres, but also take appropriate measures for endpoints such as smartphones and tablets. This is the only way to ensure comprehensive protection for their entire IT landscape. In today's digitalised working world, comprehensive basic IT protection is of great importance for your company. Simple virus protection is not enough to effectively protect your network and workstations from attacks. That's why you should rely on Medialine's comprehensive security services to protect your processes, devices and company assets from harmful influences.

Security concepts for all needs
Our IT security portfolio is geared towards comprehensive protection and state-of-the-art security concepts. This requires perfectly interlocking processes and multi-level security concepts. With Medialine, you have a strong security partner at your side:
- Consulting and conceptual design
- Training and testing
- On-site or from the cloud
- Multi-level, customised security concepts
- Protection for endpoints, communication, data and processes
Our IT security solutions in detail
Being optimally prepared for potential threats at all times while complying with legal requirements requires more than just the use of up-to-date and efficient products. Above all, it involves developing and implementing clear, multi-level security concepts to ensure comprehensive cyber security and effectively protect your systems against any attacks.
Medialine Security: Reliable protection from the cloud or on premises
As an experienced service provider in the field of IT security, we offer comprehensive support with well-designed and proven solutions. Whether you choose managed security as a comprehensive package from our CompanyCloud or as an on-premises solution at your location, Medialine is your reliable partner for the security of your company.
Your advantages
Guarantee of highest security standards
Comprehensive concepts for 360° protection
Uncomplicated and fast support in case of emergency
Consulting by certified experts
Have we sparked your interest? Please use our contact form!
Are you interested in our IT security services? Contact us for a no-obligation, personalised consultation:
Downloads and data sheets for our IT security solutions
Infrastructure & Network Security
Cloud, platform and email security
Security analyses, compliance & awareness
FAQ
A modern IT security strategy protects not only networks and servers, but also end devices, cloud systems, communications and identities. This includes firewall systems, endpoint security, email protection, SIEM solutions and security awareness training for employees.
Modern cyber attacks use complex methods such as ransomware, phishing and zero-day exploits. Companies therefore need multi-level security concepts that monitor the network, cloud, end devices and user behaviour simultaneously.
An MSSP takes over the operation and monitoring of security solutions for companies. This includes, for example, security monitoring, incident response, firewall management and vulnerability scans.
Basically, any company that uses digital systems. Security services are particularly relevant for medium-sized companies, industrial companies, financial service providers and organisations with sensitive data.
A SOC monitors IT systems around the clock for security incidents. Specialists analyse threats, respond to attacks and ensure that security gaps are closed quickly.
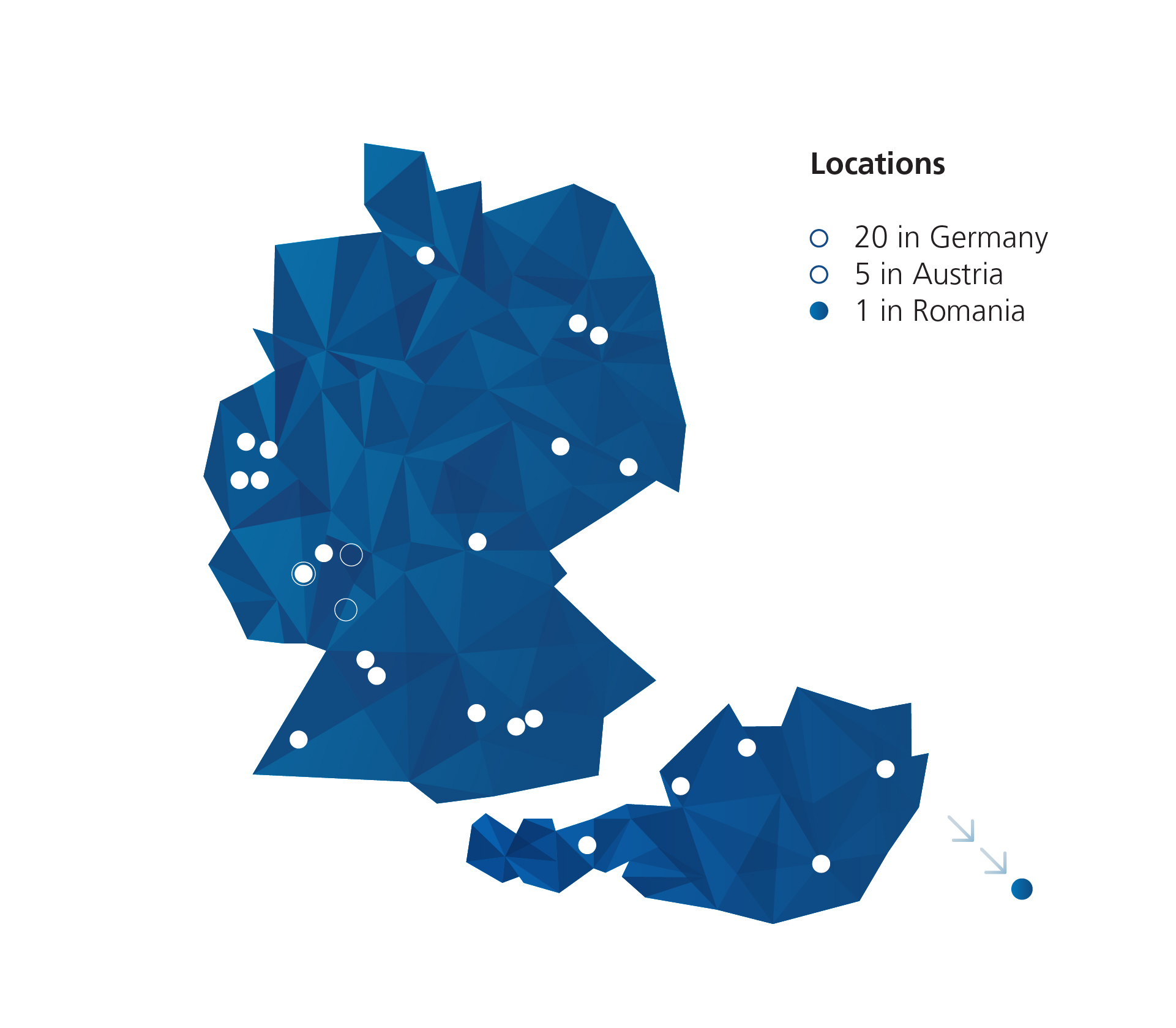
Medialine Security
Your partner for comprehensive cyber security
For over 30 years, Medialine Security GmbH has stood for sound cyber security expertise and reliable protection against digital threats. As an ISO 27001-certified Managed Security Service Provider (MSSP) based in Stuttgart, we support medium-sized companies and KRITIS organisations in securing their IT infrastructure, data and business processes in the long term. Our approach combines modern security solutions with strategic consulting – from network security and threat prevention to SOC, SIEM and CERT services to security awareness, compliance and IT governance.